![PDF] Public Key Cryptosystem Technique Elliptic Curve Cryptography w ith Generator g for Image Encryption | Semantic Scholar PDF] Public Key Cryptosystem Technique Elliptic Curve Cryptography w ith Generator g for Image Encryption | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/d4cb05572af274a00ca4425ffbf51df65279c370/3-Table2-1.png)
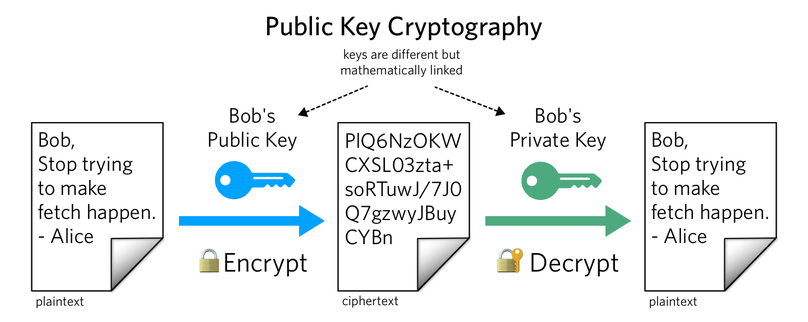
PDF] Public Key Cryptosystem Technique Elliptic Curve Cryptography w ith Generator g for Image Encryption | Semantic Scholar

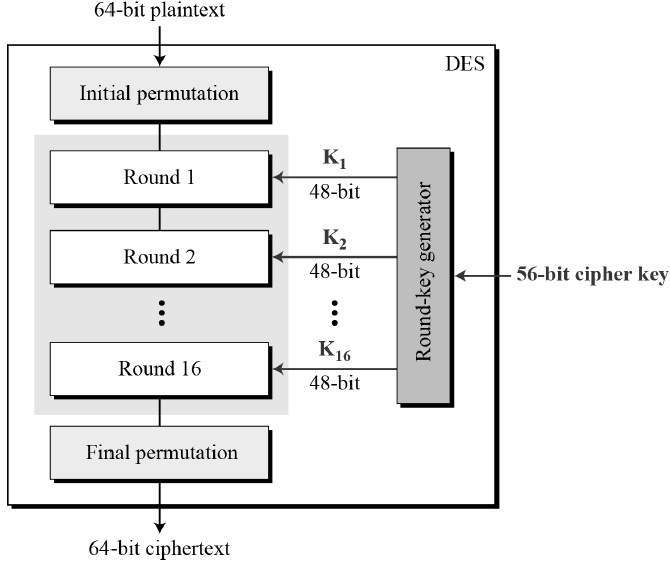
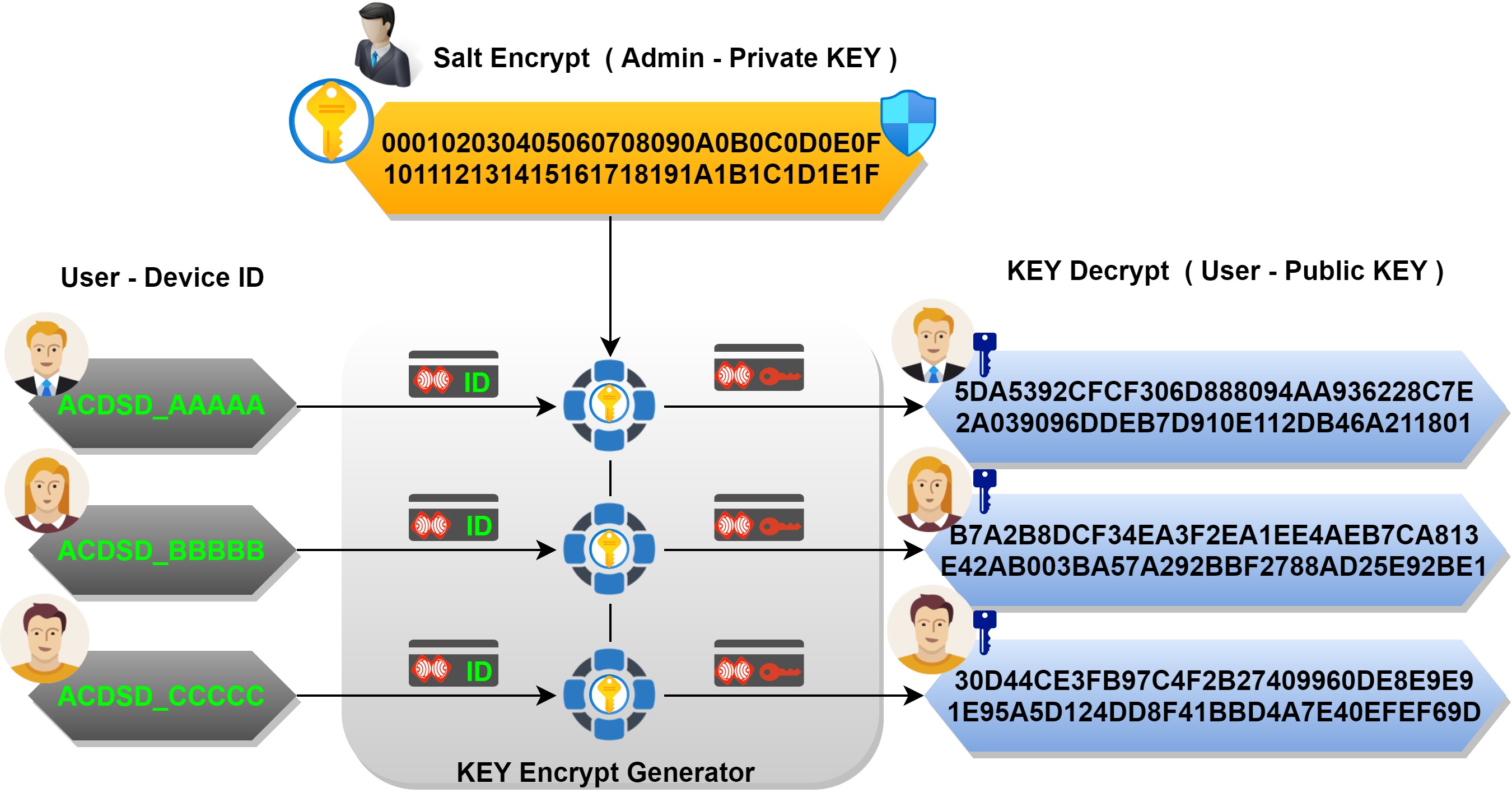
Enhanced key-generation algorithm using MRMCTT in Data encryption standard algorithm | Semantic Scholar

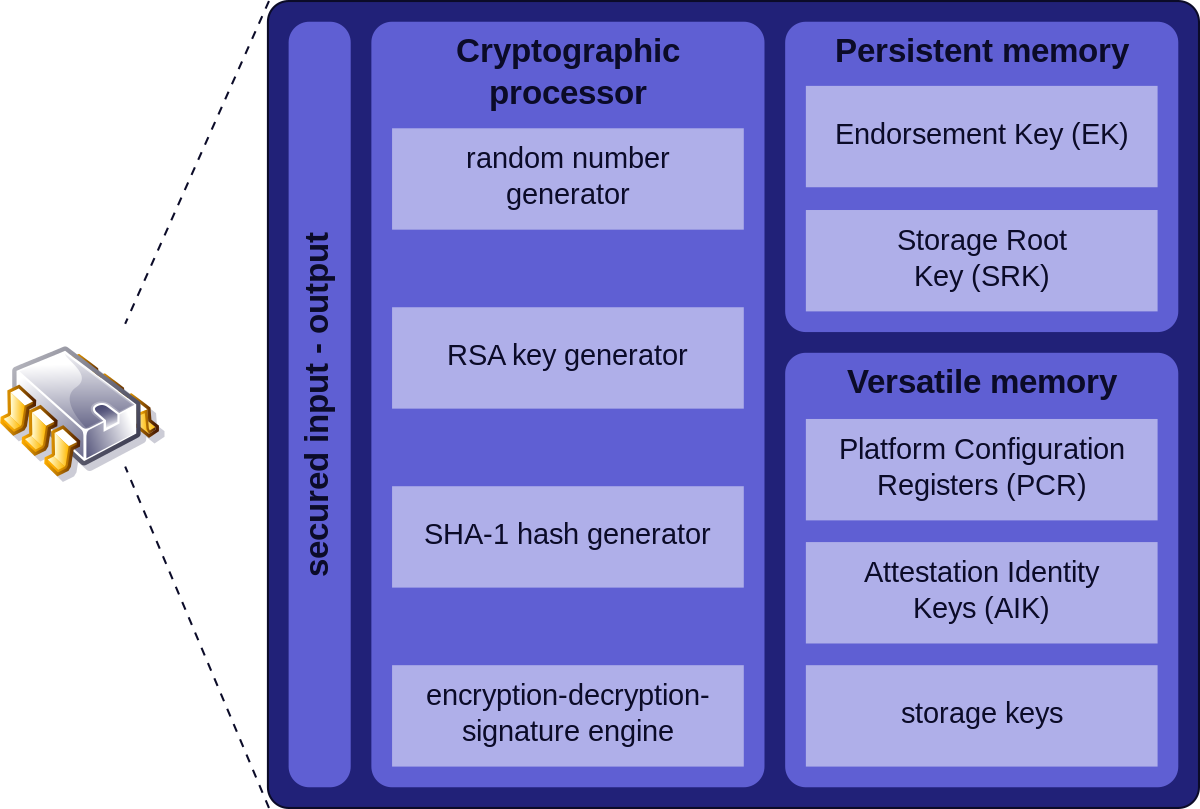
CJMCU 608 Cryptographic Key Storage Random Number Generator Signature Encryption Decryption Module|encryption keys| - AliExpress
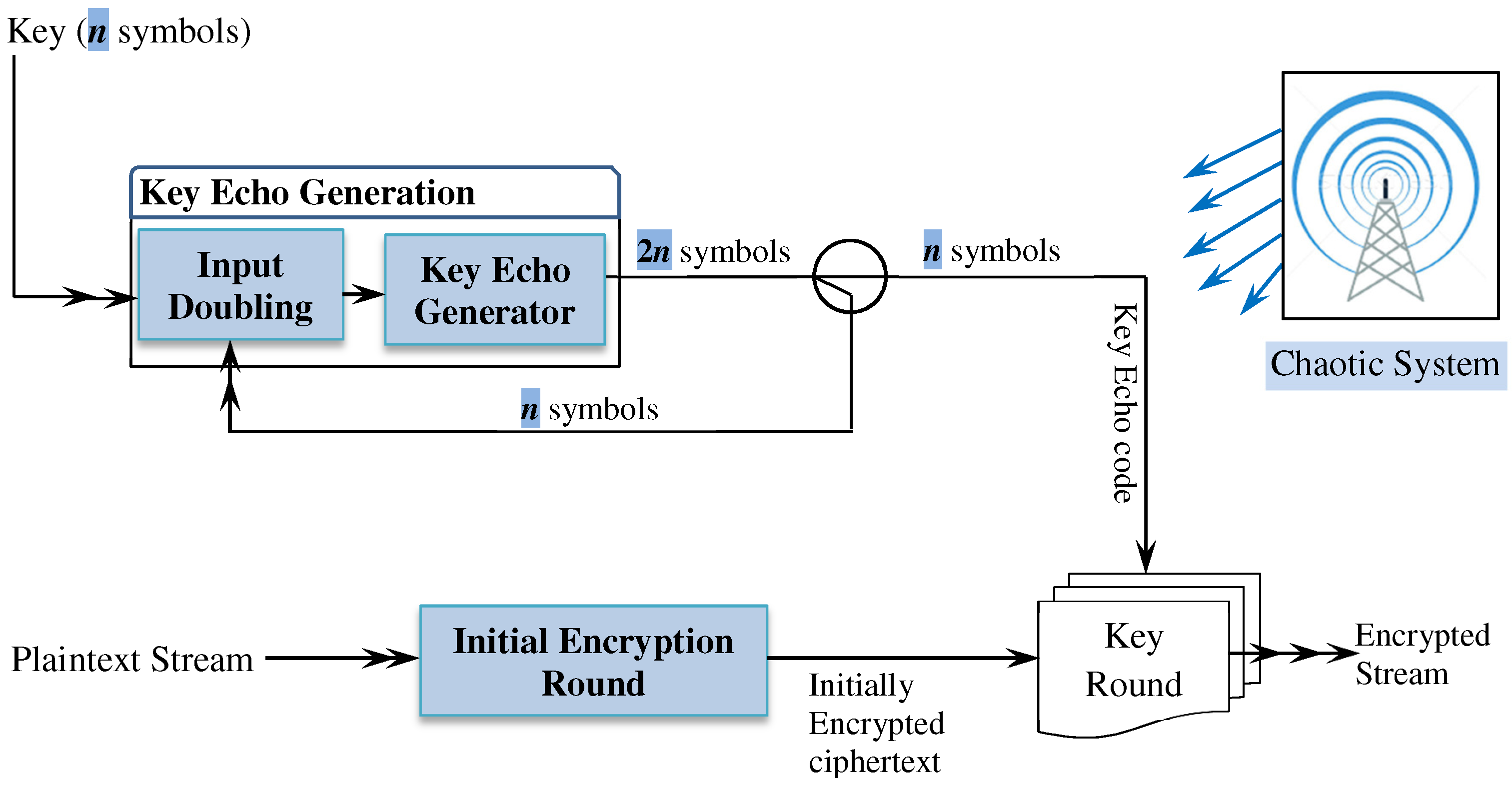
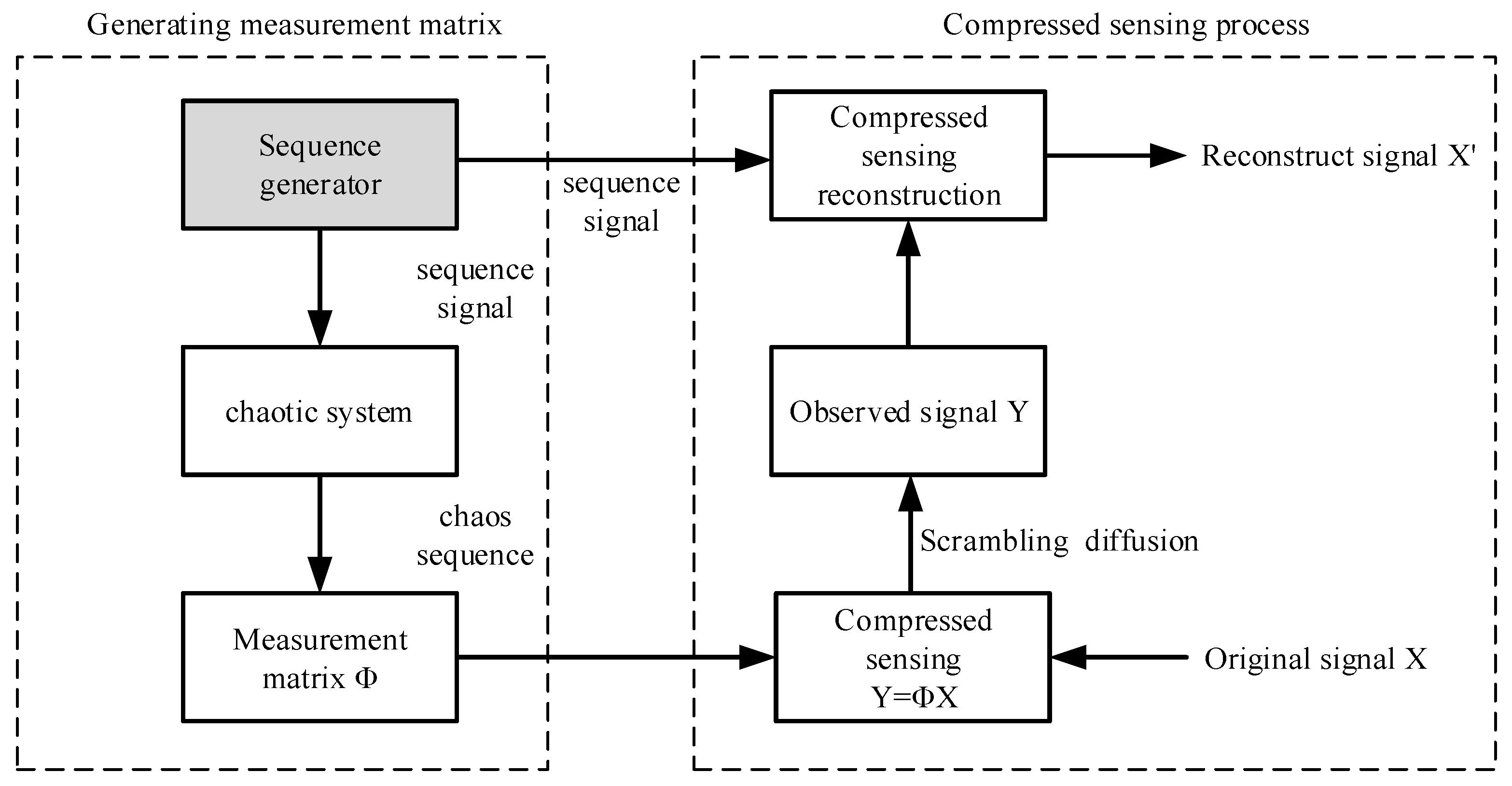
Symmetry | Free Full-Text | Light and Secure Encryption Technique Based on Artificially Induced Chaos and Nature-Inspired Triggering Method

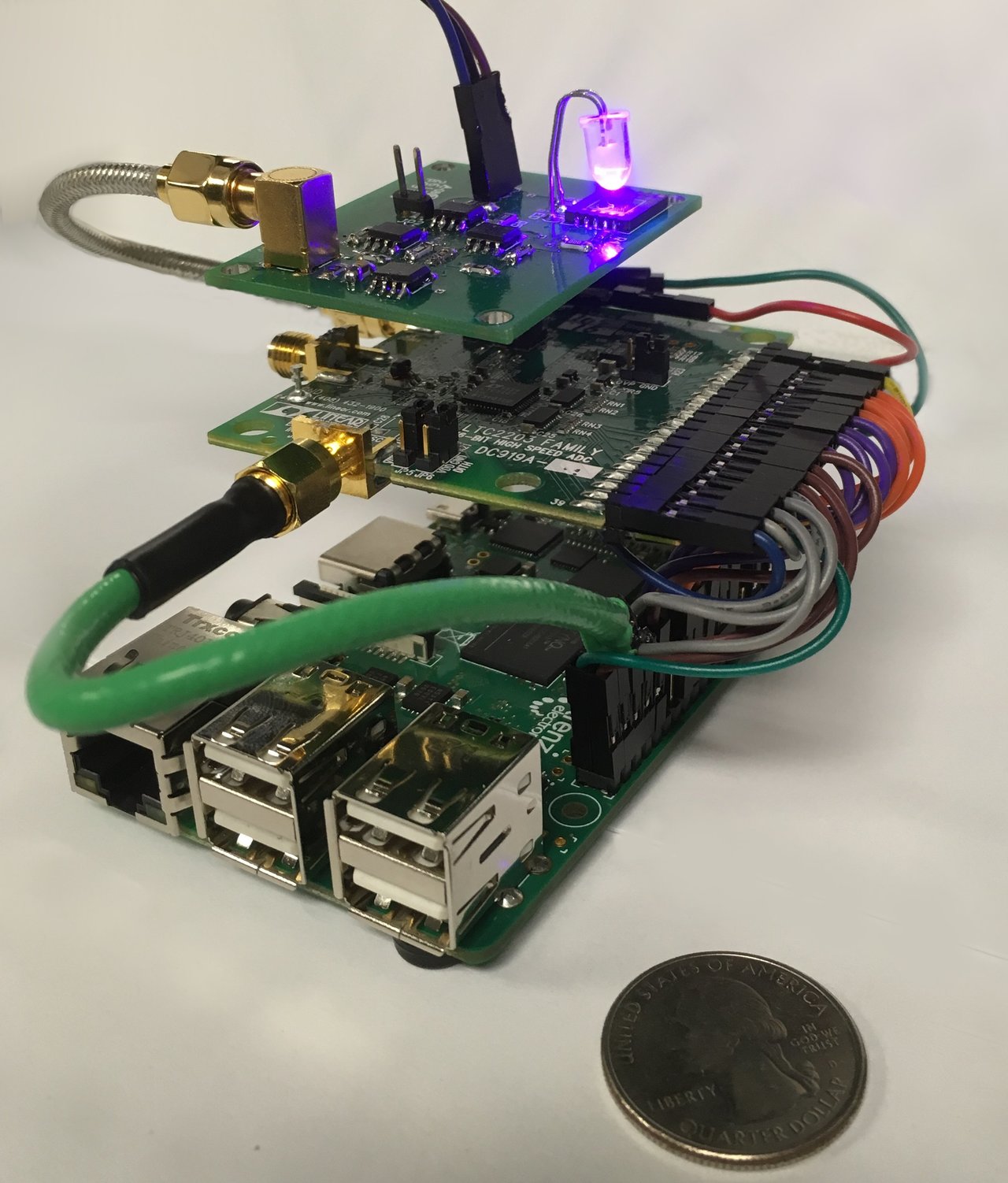
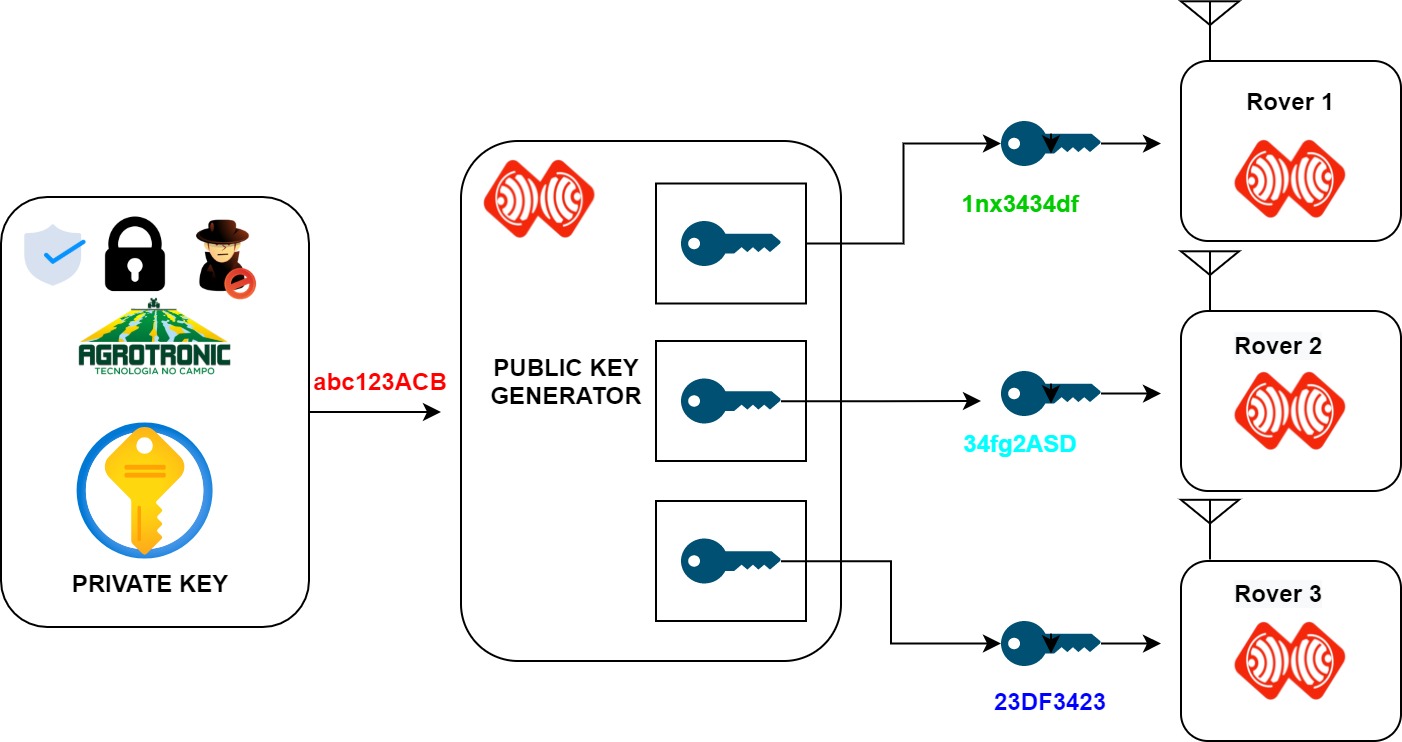
Example of an embedded encryption scheme: real time image encryption... | Download Scientific Diagram